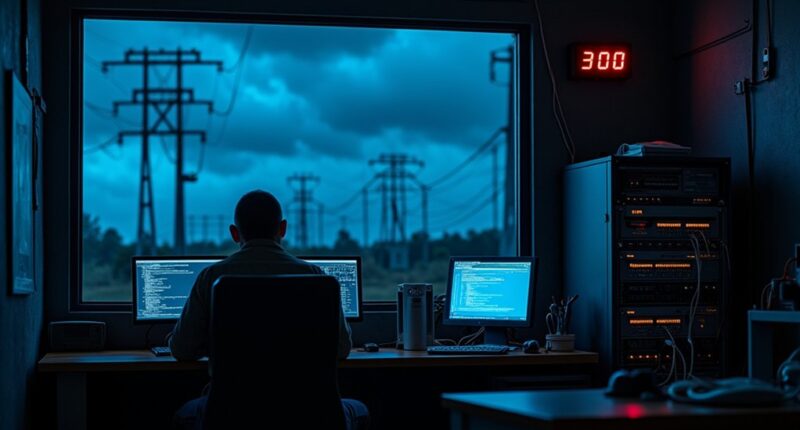
When FBI agents showed up at a tiny Massachusetts utility just before Thanksgiving last year, staff at the Littleton Electric Light and Water Departments got a nasty holiday surprise. Chinese hackers had been lurking in their systems since February. Ten whole months of uninvited digital guests. Not exactly the kind of visitors you want hanging around your electrical grid.
The culprit? A group called Volt Typhoon, a Chinese state-sponsored threat that’s been targeting U.S. critical infrastructure since at least 2021. These aren’t your garden-variety hackers. They’re sophisticated, patient, and backed by a government with resources. The group has been known to employ advanced evasion techniques to maintain long-term access to compromised networks. The breach happened because of an outdated FortiGate 300D firewall. Turns out, LELWD’s managed services provider hadn’t bothered updating the firmware. That provider? Promptly fired. Shocking.
Behind sophisticated nation-state attackers lies an embarrassingly common culprit: neglected firmware updates and lazy vendor practices.
What’s particularly weird is why Volt Typhoon bothered with Littleton, a small utility serving just 15,000 people. Not exactly the Pentagon. But vulnerability is vulnerability, and these hackers aren’t picky. They collected sensitive operational technology data and information about energy grid operations. The exfiltration enabled attackers to understand grid structure and potentially map critical components. Customer data wasn’t compromised, but that wasn’t what they were after anyway.
Dragos, a cybersecurity firm, installed sensors in August that detected unusual traffic to China. By then, the hackers had already enjoyed seven months of access. Talk about overstaying your welcome.
After the discovery, LELWD went into full damage control. They patched the firewall a week before Christmas and completely rebuilt their networks. Better late than never, right?
The incident exposes some uncomfortable truths about U.S. infrastructure security. Small utilities with limited resources and outdated equipment are easy targets. And while this particular breach was contained, it’s a warning sign. These infiltrations aren’t random – they’re part of a larger strategy. Volt Typhoon isn’t just snooping around for fun. They’re laying groundwork for potential future disruptions. This case perfectly illustrates why quarterly reviews of security protocols are the minimum standard for protecting critical infrastructure.
One thing’s for sure: this won’t be the last we hear from them.